WordPress is getting the serverless treatment, thanks to a new effort from managed WordPress hosting provider Pagely.
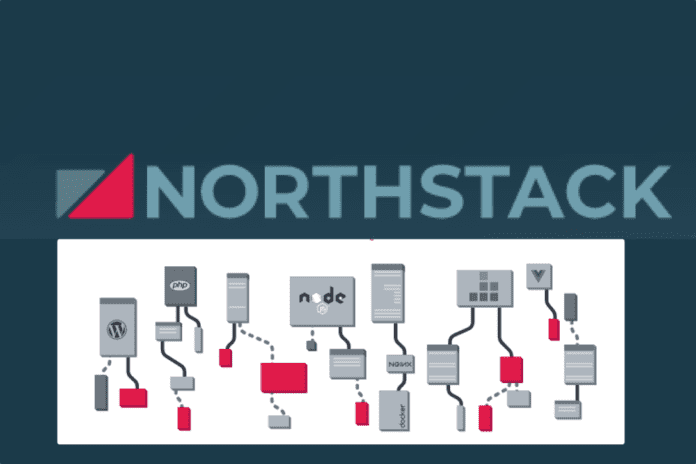
The new NorthStack platform disaggregates the usual stack that WordPress requires into a series of services that largely run on serverless infrastructure at Amazon Web Services (AWS). The NorthStack effort is an attempt to lower the fixed costs and infrastructure needed to deploy and run WordPress.
“WordPress itself is based on 12-year-old code. It does not want to be in a serverless environment,” Joshua Strebel, CEO of Pagely, told eWEEK. “WordPress wants to live on one AWS EC2 node up next to its database with everything all contained in it.”
Pagely is a privately held managed WordPress hosting provider that was founded in 2009. The company counts some big names among its high-touch customer base, including Nginx, UNICEF, Visa, Disney and Comcast.
WordPress is one of the most widely deployed blogging and content management systems (CMS) on the internet. The code is updated regularly, with the most recent release being the 4.9.8 maintenance update that became generally available on Aug. 2. WordPress requires a standard LAMP (Linux, Apache MySQL, PHP) stack on which to run. The Pagely NorthStack approach does not rewrite WordPress for a different stack; rather it takes a different approach to deploying and running the required infrastructure.
How It Works
Strebel said NorthStack uses the Amazon Aurora Serverless database alongside Docker containers to containerize various aspects of the WordPress hosting platform.
“It’s like a bridge between the old legacy WordPress code base and the modern stack,” he said. “What we didn’t do is actually go in and rewrite WordPress as AWS Lambda functions. That would be a suicide mission that I wouldn’t wish on my worst enemy.”
The way the system works is it is deployed across different containers that can scale up or down based on demand, Strebel said. The promise of serverless, also known as Functions as a Service, is that services are only running when called on. With a website, there are a number of elements that always need to be available and running, such as DNS resolution. As such, NorthStack runs the AWS Route 53 DNS service in a persistent way and when a web browser hits the DNS, it can trigger additional capacity as needed.
“So if a request comes in and there isn’t an active container running, we can pull a cached version out, serve that to the client and then start the ramp-up process in the back end, and it might take three or four seconds for that container to wake up,” he said.
While NorthStack is largely serverless, there is still also a need for a persistent storage element for WordPress data, which is where Pagely uses the Amazon S3 storage system. The live filesystem for WordPress itself that includes the PHP configuration runs on Amazon Elastic File System (EFS) volumes, which scale up or down based on demand.
“There’s always going to be some persistent usage even if it is very minimal,” Strebel said. “But what we’ve tried to do with NorthStack is measure things in small units and only on consumption.”
Strebel said that, for example, NorthStack measures CPU time down to the second, such that if a user gets a request coming in to their WordPress site, it will dynamically open up a few worker processes and make the database query. After that the worker processes disappear, Strebel said the WordPress site owner is no longer paying for the other 59 minutes of database time if that site is only calling the database once an hour.
“We tried to get consumption increments as small as possible to keep the billing low,” he said.
NorthStack is currently in a limited private beta with general availability set for 2019.
Sean Michael Kerner is a senior editor at eWEEK and InternetNews.com. Follow him on Twitter @TechJournalist.